Cơ hội cho nữ sinh muốn học nghề cắt gọt kim loại, làm việc tại Đức: Ra hạn đến 31/1


Ngày 15/4/2024, tại văn phòng Hiệp hội Giáo dục nghề nghiệp và Nghề công tác xã hội Việt Nam, đoàn cán bộ cao cấp trong lĩnh vực giáo dục của Chính phủ Phần Lan thăm và làm việc với Hiệp hội Giáo dục nghề nghiệp và Nghề công tác xã hội Việt Nam (VAVET&SOW).

Ngày 25/05/2024, tại Hà Nội, AHK Việt Nam cùng Đại sứ quán Đức, Viện Goethe, GIZ, DAAD đồng phối hợp tổ chức một sự kiện dành cho sinh viên và người lao động Việt Nam có mong muốn học tập và làm việc tại Đức.

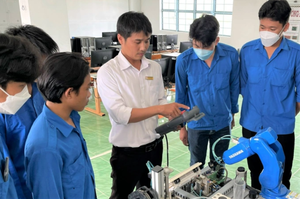
Những học viên tốt nghiệp đầu tiên của Chương trình “Cơ chế đối tác thúc đẩy giáo dục nghề và Di cư lao động định hướng phát triển” (PAM) bước vào hành trình tới nước Đức. Điều này đánh dấu sự khởi đầu một chương đầy hứa hẹn cho lao động lành nghề Việt Nam và hệ thống giáo dục nghề nghiệp của Việt Nam trên trường quốc tế.

Ngày 06/04/2024, Văn phòng đại diện Hiệp hội Giáo dục Nghề nghiệp và nghề Công tác Xã hội Việt Nam tại thành phố Hồ Chí Minh phối hợp với Trường Cao đẳng Kiên Giang; Viện Nghiên cứu, Đào tạo và Phát triển Tài nguyên Giáo dục Mở; Đại diện Google tại Việt Nam tổ chức tọa đàm ‘Chuyển đổi số - khung năng lực số và các điều kiện xây dựng nhà trường số’.